Phishing emails are not just an IT problem—they are a real business risk for businesses across Chippewa and Wisconsin, including our CEDC investors. Cybercriminals are getting more sophisticated at sending fake emails that appear to come from trusted local organizations, including the CEDC. Some even impersonate board members or business owners, using their names and email addresses. These messages are designed to prompt quick action—often clicking a link or opening an attachment—before you notice the warning signs. Scammers know you are more likely to trust messages from familiar names or organizations like us. They often:
- Spoof the sender’s name – For example, using a board member’s name but sending from a free email account like Gmail instead of our official domain.
- Create urgency – Messages such as “We need you to pay this invoice now” or “Quick favor, are you in the office?” push you to act fast.
- Use fake links – Links may appear to go to CEDC or a partner but actually lead to phishing sites designed to steal passwords.
- Attach malicious files – PDFs, Word documents, or ZIP files may contain malware.
If you’re surprised to see a message “from” a board member, business owner, or CEDC staff-contact asking you to click, pay, or share sensitive information, slow down. That surprise is often your first red flag. Most phishing emails share a few telltale traits so watch for:
- Generic greetings: “Dear customer” or “Hello user” instead of your name, especially from organizations that usually personalize communication.
- Urgent or threatening language: Warnings that your account will be suspended, that you owe money, or that you must act immediately.
- Strange sender address: The display name may look correct, but the email address is misspelled or uses a public domain rather than the official organization domain.
- Suspicious links: Hover over links to check that the web address matches the organization it claims to be from.
- Poor spelling or grammar: Legitimate organizations typically avoid obvious mistakes.
- Unsolicited attachments: Files you did not request, especially when paired with urgent language.
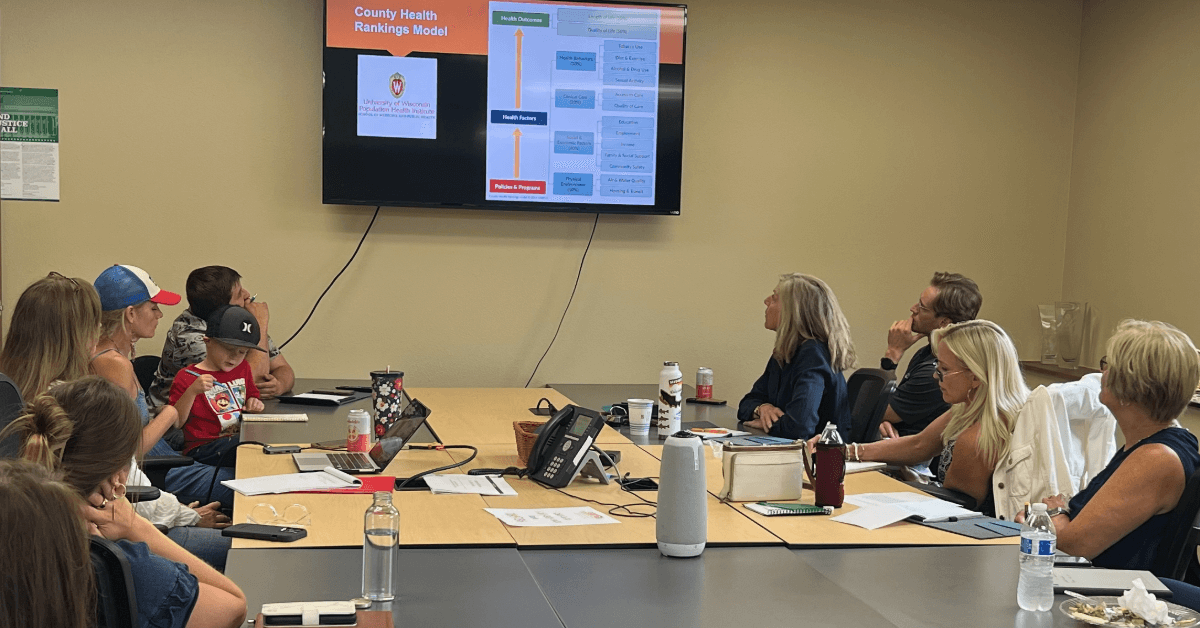
Even the best spam filters and security software cannot catch every phishing email, especially highly targeted ones that use real names and local organizations. Even “smaller” events—like paying fake invoices or gift card scams after a phishing email—can quietly drain tens of thousands of dollars from a local businesses tight budget. Human awareness—knowing what to look for and how to respond—is one of the strongest defenses our local business can have. Businesses that attend on going education and seminars such as our BEAR Lunch and Learns tend to experience fewer successful attacks, less downtime, and stronger trust from their customers and partners.
Phishing emails can be devastating for many Chippewa businesses big and small because even one bad click can trigger losses that many local shops simply cannot absorb. The damage is not just technical; it hits your bank account, your ability to operate day‑to‑day, and the trust our community has in your business. This is exactly why we host our BEAR Lunch & Learns and partner with industry experts to provide practical, plain-language guidance that helps your businesses anticipate risks, stay operational during disruptions, and recover quickly. Protecting your operations safeguards jobs, investment, and the long-term stability of the local economy. Past CEDC BEAR Lunch and Learn topics have included:
- Cybersecurity & Ransomware Preparedness
- Workforce Recruitment Strategies
- Employee Retention & Workplace Culture
- Training Within Industry (TWI)
- Economic Outlook & Market Trends
- Succession Planning for Business Owners
We are currently partnering with The Dirks Group on April 14th to host a BEAR Session-Business Continuity & Disaster Recovery Planning —an executive-level seminar designed for business owners and senior leaders that want to gain practical, clear, and actionable guidance to prepare for cyber incidents, operational outages, and unexpected disruptions.