In today’s digital age, the importance of cybersecurity cannot be overstated, especially for Department of Defense (DoD) manufacturers in the Chippewa Valley. These manufacturers are crucial to national security, making them prime targets for cyberattacks from state-sponsored actors, organized crime groups, and opportunistic hackers. A successful cyberattack on Western Wisconsin’s DoD manufacturers could have catastrophic consequences, potentially compromising sensitive defense information, disrupting operations, and endangering national security.
To address these critical cybersecurity needs, the Wisconsin Procurement Institute and UW-Stout Manufacturing Outreach Center (MOC), in collaboration with Chippewa Valley Technical College (CVTC) and the Chippewa Economic Development Corporation (CEDC), hosted a BEAR Discussion event. This event tackled the pressing challenges faced by the manufacturing sector. Expert speakers, including Stephen Casselman, IT-Network Specialist Instructor at CVTC’s Center for Cyber Defense, Ron Thomas, Senior Management Engineer at UW-Stout MOC, and Matt Frost, Government Contract Specialist at the Wisconsin Procurement Institute, shared valuable insights and experiences.
Held at the CVTC Campus, the BEAR Discussion covered crucial topics such as automation and operational technology, providing attendees with insights into how these innovations can enhance efficiency and productivity. Over a dozen participants gained practical knowledge on integrating cutting-edge technologies into their operations and discussed compliance with government regulations, including Cybersecurity Maturity Model Certification (CMMC) requirements. Meeting these stringent cybersecurity standards is essential not only for securing contracts but also for avoiding legal liabilities and reputational damage.
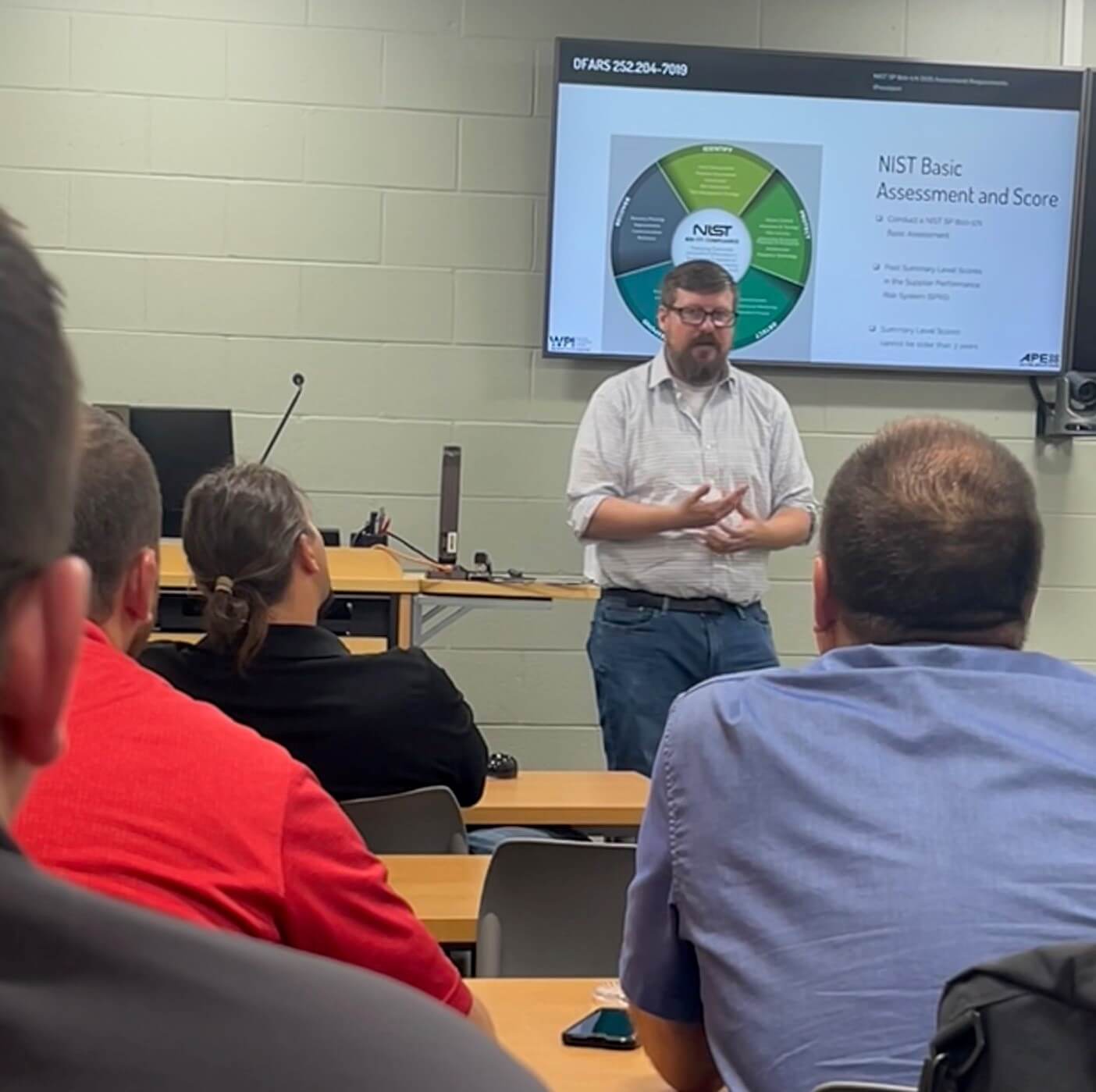
Matt Frost addressed a key component of the event: an introduction to cybersecurity requirements for federal and defense contracting. He provided manufacturers with essential information to comply with cybersecurity regulations, protect their operations, and maintain eligibility for government contracts. Participants learned the necessary steps to meet compliance standards, safeguard sensitive data, and secure potential federal and defense contracts.
CEDC Board Member Ken Pearson and CVTC’s Stephen Casselman led a discussion on CVTC’s Center for Cyber Defense, which is designated by the NSA as a “Center for Academic Excellence in Cyber Defense Education.” This center plays a pivotal role in strengthening national information infrastructure and offers cybersecurity resources to students, faculty, the community, and local manufacturers. The Cyber Range at CVTC is also available to help industry partners simulate real-world cybersecurity scenarios, preparing them for future digital challenges.
Ron Thomas from Manufacturing Outreach highlighted the shift towards greater automation and the accompanying increase in data exchange, which necessitates enhanced security measures. Local DoD manufacturers handle vast amounts of sensitive and classified information, including blueprints, defense strategies, and advanced technologies. A cybersecurity breach could lead to the theft of this critical data, enabling adversaries to replicate or counter U.S. military capabilities. Prioritizing cybersecurity is essential to protecting this information and ensuring it remains secure.
As cyber threats continue to evolve, so too must the cybersecurity measures employed by Chippewa Valley manufacturers. This requires continuous updates, regular risk assessments, employee training, and the adoption of advanced security technologies. By staying proactive in the face of evolving threats, these manufacturers can reduce the risk of successful attacks and maintain a robust defense posture. For DoD manufacturers, cybersecurity is not just a technical requirement—it’s a strategic imperative. By prioritizing cybersecurity, these manufacturers play a crucial role in securing the future of our nation. Events like the one hosted by CEDC and CVTC are vital in equipping them with the tools and knowledge needed to stay ahead in the cybersecurity battle.